FORMOBILE: Life After the Mobile Forensics Project
PPHS led the Communication and Dissemination efforts of the FORMOBILE project, which concluded in April 2022. The project’s website has now been taken offline, but you can find the key outputs listed here.
The three-year project brought myriad developments, research and tangible, concrete outputs.
Thankfully, there are several ways the different practitioners, stakeholders and partners can continue to reap benefits and value from the project and its key outputs.
This article will briefly describe several main points and identify the key contact people for the specific areas.
The FORMOBILE team has created an extensive report detailing many of the project’s tasks and outputs to supplement this news piece. The document is the output of the FORMOBILE End Conference held at the Netherlands Forensic Institute on the 28th and 29th of April 2022.
To help illustrate the key points described below, we have also prepared a leaflet to emphasise the critical matters.
Continued Dialogue
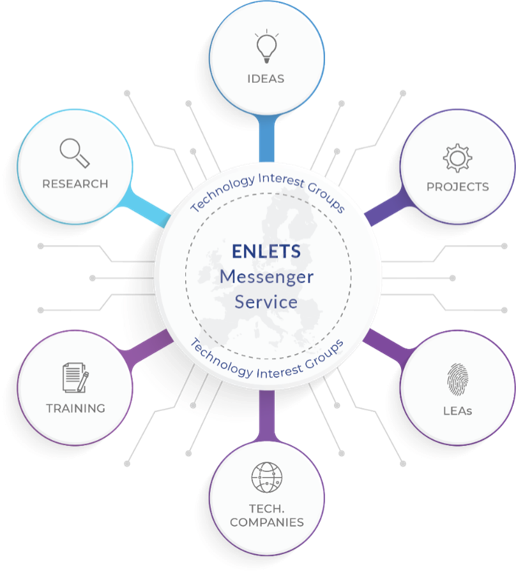
To help with the transition following the FORMOBILE project, the European Network of Law Enforcement Technology Services (ENLETS) has offered a dedicated space on their ENLETS Messenger Service for tool developers and LEAs to engage. The free solution provides a safe, encrypted chat experience through a dedicated mobile application and web browser service. To access the service, please complete this form.
Mobile Forensic Tools
Within FORMOBILE, the team worked on 12 individual tools. From the proposal phase – even before the project was granted – the team had an idea of how the exploitation of tools would work. The goal was to simplify the process and create as many tools as possible to benefit law enforcement in the short to medium term. Notably, by involving a commercial partner that is widely recognised in the domain within the project, the team was able to filter outputs directly into the MSAB portfolio of tools – overcoming one of the biggest obstacles common in many research projects – taking an idea to market.
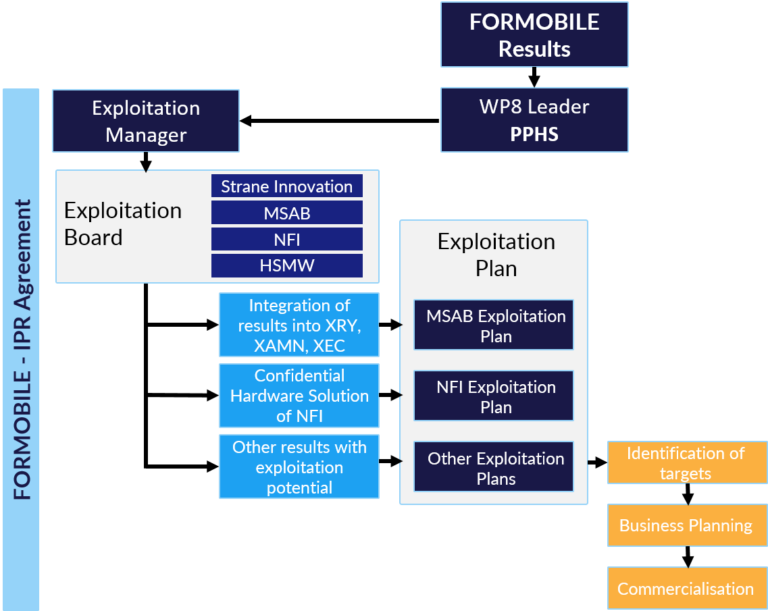
Although there were no commercial opportunities to start new ventures during the project, several of the tools can be extended and improved, and the team is in contact with EACTDA to explore these.
Moreover, the FORMOBILE coordinator, Hochschule Mittweida, is keen to improve several of the ‘open source’ solutions and will be engaging with EUROPOL to explore options for adding several tools to the EUROPOL Tool Repository for Law Enforcement Agencies. FORMOBILE has its own page on Github, which can be seen here: https://github.com/FORMOBILE
FORMOBILE - A Tool by Tool Exploitation Overview
RAMxTRACTOR – A confidential tool. Contact Coert Klaver c.klaver@nfi.minvenj.nl for more details.
CLOUDxTRACT – Part of MSAB’s XRY suite, but will also be provided to EUROPOL as an open-source solution. Contact Prof. Dr Dirk Pawlaszczyk at pawlaszc@hs-mittweida.de for more information.
CLONEaCQUIRE – Part of MSAB’s XRY Suite. The solution is available and will be further developed by MSAB.
eMMC emulator – Confidential tool for specialists, contact Coert Klaver c.klaver@nfi.minvenj.nl for information.
RAMdCODER – Confidential tool for specialists, contact Mike Dickinson mike.dickinson@msab.com for information.
Antiforensic System – Plans to make part of the standard MSAB XRY kit. Contact Mike Dickinson mike.dickinson@msab.com for more details.
Dump Decoder – Part of MSAB’s XRY suite, will be improved and developed by MSAB.
Semantic Analyser – A tool that has huge potential but requires continued development. Hochschule Mittweida manages the solution, please contact Prof. Dr Dirk Pawlaszczyk pawlaszc@hs-mittweida.de for more information.
Malware Analysis Platform – A standalone tool that is under development. Please contact Andreas Richl at andreas.Richl@ZITiS.bund.de for more information.
FORMOBILE Visualiser – Part of MSAB’s XAMN platform. The solution will be improved and developed continuously.
Dump Analysis Tool – Part of MSAB’s XAMN platform. The solution will be improved and developed continuously.
FORMOBILE Mobile Forensic Training
Throughout the project, the training topic was in great demand. There was significant interest from various corners of the domain, and FORMOBILE was able to support this need.
Within the project, FORMOBILE delivered three pilot courses that are now publicly available, plus a specialised workshop for forensic laboratories – which will also be facilitated after the project.
The European Cybercrime Training and Education Group (ECTEG), will build from the foundations of the work completed in FORMOBILE through their dedicated project – MobiFor. The excellent aspect here is that a pivotal partner involved in FORMOBILE – the Norwegian Police School – is also a member of ECTEG and will be responsible for the improvements and development of the other materials started under FORMOBILE.
The annual workshop is a unique event that will continue to run at the Netherlands Forensic Institute, and it will build on the efforts of the FORMOBILE project and provide dedicated training for experts across the EU. To express your interest in the annual workshop for forensic laboratories, please contact ECTEG.
Standards
The national standardisation institute of Austria – Austrian Standards International – led the highly successful standard work of the FORMOBILE project.
A collaborative effort of over 50 experts from 30+ organisations contributed to a pivotal document that promises to change the face of mobile forensics within the EU. The CEN-CENELEC Workshop Agreement (17865) is a landmark document that can help LEAs and other actors in the mobile forensic investigation chain address the pertinent points related to processes, personnel, technology and legal and ethical matters.
FORMOBILE worked hard to prepare a comprehensive document, but it would not have been possible without input from experts across the domain – including industry competitors. All collaborated for the ‘greater good’, and resulted in a valuable output that will benefit stakeholders across the industry.
CWA 17865:2022, Requirements and Guidelines for a complete end-to-end mobile forensic investigation chain, is publicly available for download.
Final Conference Videos
With this article and the materials that are linked, hopefully, you will have all the information you require. However, if you need any of your questions addressed, please contact communicaton@formobile-project.eu.
Check Out Our Latest Activities

Launching Sparks in the Dark: A New Ally in the Fight Against Child Sexual Abuse
Every year, millions of children worldwide face the horrors of child sexual abuse and exploitation (CSAE), a pervasive issue that demands urgent action. In response to this critical issue, ‘Sparks

New Security Initiative: Threats Observatory for the Wielkopolska Region
As the Polish Platform, in addition to the implementation of numerous national and European projects, we are also involved in other forms of increasing safety. One of these is the

Cooperation Between Uniformed Services and Businesses in Protecting Against Cyberattacks
Discussions on the importance of improving the resilience of businesses and organisations against cyber threats have become a norm. Yet, we often overlook the importance of reporting cyber incidents to

Radicalisation – Rebellion in Extreme Form
Although radicalisation is stereotypically associated with certain groups, it can affect almost everyone. Since extremism contributes to the destruction of the social fabric, it is critical we counteract problems before

Shaping the Next Generation of Security Solutions – The Impact of APPRAISE
The APPRAISE project, a pioneering initiative to improve the cooperation between public and private security operators, has recently concluded. Now is the opportune moment to reflect on the significant results

CINTiA 2024: We are opening registration for companies!
The third edition of the analytical conference CINTiA 2024 (“Criminal Intelligence – New Trends in Analysis Conference 2024”) will take place in Krakow, Poland on September 24-26.